Introduction
Protecting sensitive company information is more than just a technical requirement — it’s a business necessity. Customer records, financial data, intellectual property, and strategic plans are all critical assets. Exposure can lead to financial loss, reputation damage, and legal consequences. The best ways to protect sensitive company information combine technology, policies, and people, starting with knowing what data is most valuable.
In this guide, you’ll learn practical strategies to safeguard your organization’s most critical information, reduce risk, and build trust with employees, clients, and partners.
Why Protecting Sensitive Company Information Matters
Every company, from startups to global enterprises, handles sensitive information. This includes customer identifiers, employee records, financial information, intellectual property, trade secrets, and strategic business plans. Sensitive company information is any data that, if leaked, altered, or stolen, could harm your business or stakeholders.
Threats to sensitive information can come from cybercriminals, insider misuse, accidental disclosure, or physical loss. The best ways to protect sensitive company information are practical, systematic, and achievable with planning and investment.
Start With Understanding Your Data
What Qualifies as Sensitive Information?
Not all data is equally at risk. Examples of sensitive company data include:
- Customer personal and financial records
- Employee records, including payroll and identification
- Intellectual property and trade secrets
- Strategic business plans and internal communications
- Regulatory data subject to compliance requirements
Identifying and classifying your sensitive data is the first step in protection. It helps you decide which data needs strict security measures and which can be stored or archived with fewer restrictions.
Organizational Strategies to Protect Sensitive Company Information
Data Classification and Inventory
A data classification program labels information based on sensitivity. Highly sensitive data receives stricter controls, while less critical information does not consume unnecessary security resources.
Create Clear Policies and Protocols
Documented policies help employees understand how to handle sensitive company information. Policies should cover data storage, access, transmission, retention, and secure disposal. Clear rules reduce guesswork and improve accountability.
Appoint a Data Protection Officer
For businesses handling large volumes of personal or regulated data, appointing a dedicated Data Protection Officer (DPO) ensures compliance with privacy regulations. A DPO oversees policies, trains staff, and ensures processes align with legal frameworks.
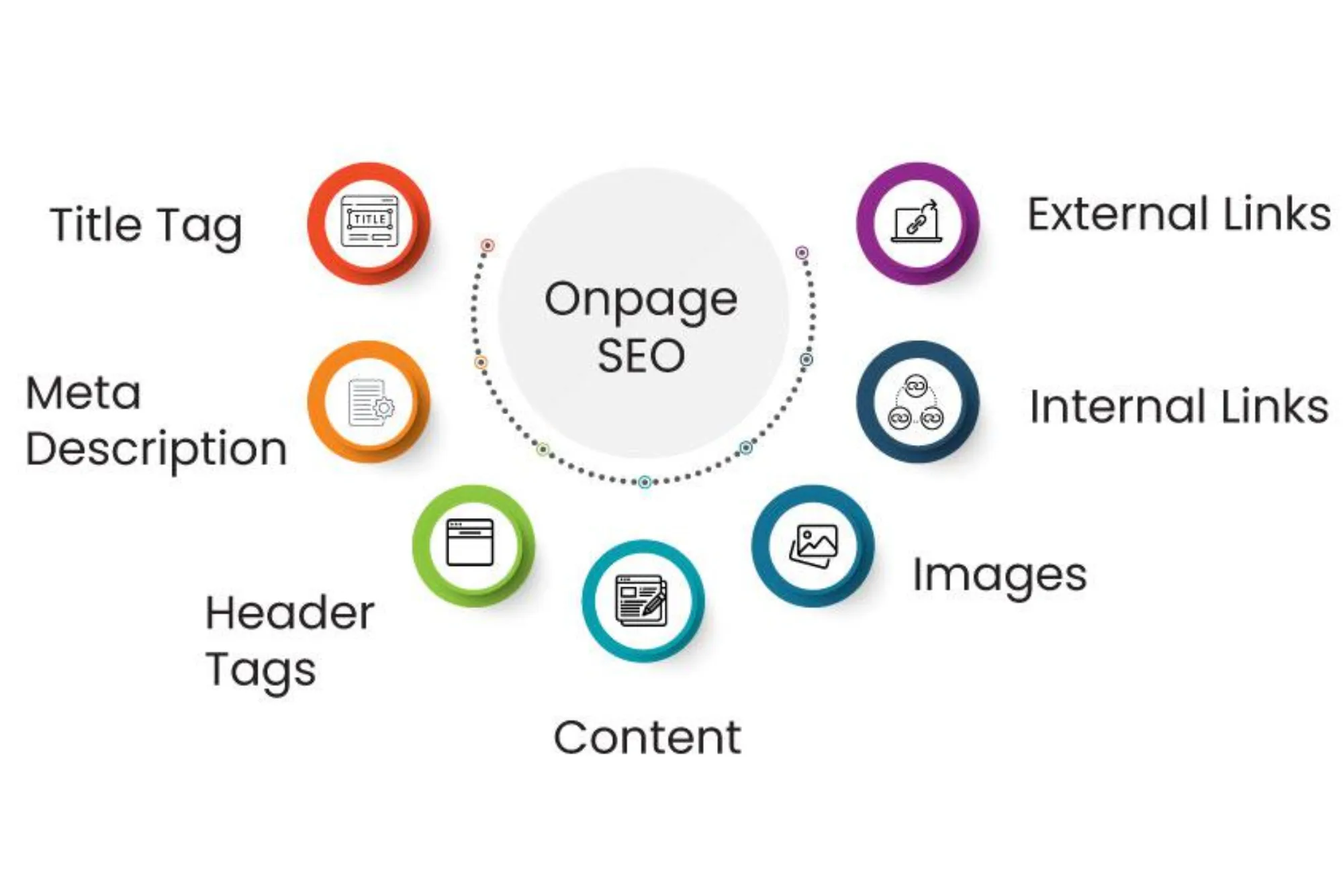
Technical Defenses Every Business Should Have
Strong Access Controls
Limit access to sensitive company information to employees who genuinely need it. Role-based access control (RBAC) reduces unauthorized use and accidental disclosure.
Encryption Everywhere
Encrypt data both at rest and in transit. Encryption ensures that even if data is intercepted, it remains unreadable to unauthorized users.
Multi-Factor Authentication (MFA)
Passwords alone are no longer sufficient. MFA requires a second verification step, such as a code sent to a mobile device or a biometric scan, greatly improving access security.
Zero Trust Architecture
Zero trust security assumes no user or device is automatically safe. Every access request is verified before granting entry to sensitive systems or data.
Secure Backups and Disaster Recovery
Regular backups and a tested disaster recovery plan ensure you can regain control after a breach or system failure. Offline or immutable backups prevent ransomware from encrypting your critical files.
Training and Culture Change
Train Employees on Security Awareness
Human error is one of the biggest risks to sensitive information. Regular training on phishing, password security, and device safety helps build a security-conscious workforce.
Simulated Phishing and Practice Drills
Mock phishing exercises teach employees how to spot suspicious emails and links, reducing the risk of social engineering attacks.
Confidentiality Agreements and NDAs
Require employees, contractors, and consultants to sign non-disclosure agreements (NDAs) to legally protect sensitive company information.
Physical Protections Matter Too
Secure Paper Documents
Lock file cabinets, shred sensitive papers, and limit physical access to storage areas. Physical copies are still at risk if not properly secured.
Access Controls for Offices
Badge entry systems, visitor logs, and locked server rooms prevent unauthorized individuals from accessing sensitive information.
Ongoing Maintenance and Monitoring
Regular Security Audits
Audit data access, test systems for vulnerabilities, and review policies periodically. This ensures protection strategies evolve with new threats and business changes.
Continuous Monitoring and Alerting
Monitor systems for unusual activity, such as logins from unexpected locations or large data exports. Alerts help respond quickly to potential breaches.
Protect Your Business Today
Protecting sensitive company information is an ongoing commitment. By identifying critical data, applying strong access controls, using modern security technologies, and fostering a culture of awareness, businesses can significantly reduce risk.
FAQs
What is sensitive company information?
It includes any data that could harm the business if exposed — such as customer details, financial records, trade secrets, and strategic plans.
How do you limit access to sensitive information?
Use role-based access control to ensure employees only access data necessary for their job.
Why is encryption important?
Encryption makes data unreadable to unauthorized users, keeping it secure even if stolen or intercepted.
How often should companies update their security policies?
Review and update policies at least annually or whenever major business or technology changes occur.
What role does employee training play in data security?
Training helps employees recognize threats, avoid mistakes, and adopt best practices to protect sensitive information.
How to Secure Online Transactions for Your Customers – Ensuring safe online transactions is crucial for building trust. Use SSL encryption, secure payment gateways, and two-factor authentication. Regularly update software and educate customers on phishing risks to protect sensitive data and create a safe shopping experience.